Dealing With Demands to Preserve Evidence
Submission Date
Question
Recently a law firm from Albany sent us a memo claiming to represent the plaintiff in a civil suit and informing us of their intent to have a subpoena issued for access to our security footage on a particular day. The memo asked us to preserve the footage in question in expectation of the subpoena. They did not specify an area of the library or a time for the footage.
I would like to know what limitations and obligations we have in this civil matter with regard to patron privacy.
Answer
Before we dive into this, a word of caution: sometimes “law firms” are not always what they seem.
Because I am writing this in 2025, you might assume I am starting with the caution because “deep fakes” are out there pretending to be lawyers, politicians, and your grandchildren stranded on the road in Arkansas.[1]
But actually, this has been a problem for a long time, even before someone could use PageMaker[2] to cobble up a fake law firm letterhead.
So, before a library (or any cultural institution) leaps into response mode on a “lawyer letter,” it is wise to do what the member is doing: exercise a little healthy skepticism.
In this case, it is good to verify that the firm and lawyer are real, and that the firm you’ve verified actually sent this.
Now, if there is any chance that the legal matter in question could involve a claim against your institution, it is wise for your lawyer to do this. I am not saying that to drum up work for my siblings at the bar,[3] but because the initial outreach to the requesting firm could result in providing information they are not entitled to, and it could put your institution at risk. Using your attorney to make the contact will reduce this risk.
The attorney can, at the same time, assess if the demand has teeth (as in, can the requirement to preserve the footage be enforced?), and advise on next steps. As part of that exercise, the attorney will evaluate this from the perspective requested by the member: patron privacy.
The first part of that evaluation is standing under the transparent elephant in the room: FOIL.[4] If a record is available under FOIL, a person doesn’t have to get a subpoena to demand a copy; they can just request the record, and the library has 5 business days to get them an initial response to the request.
Of course, FOIL is not a magic wand that brings immediate access to all records; there are all sorts of exceptions to what must be disclosed under it, and those exceptions include library user records.
This brings us to the next consideration: what your library has defined as “library user records.” While the law in New York governing the confidentiality of library user records[5] does not mention security footage, it allows libraries to include such records in their own definition. If a library’s “Confidentiality of Library User Records Policy”[6] lists security footage—or security footage in certain areas—as a “user record,” the content cannot be disclosed without a written release from the relevant patron(s), a court order, or a subpoena.
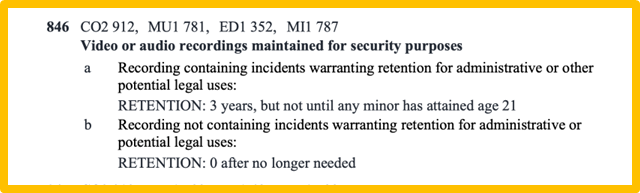
The next thing to consider is your library’s practice of retaining security footage. In New York, security footage can be FOILed, but there is no obligation for an agency to retain such footage unless there is a “potential legal use.” This “0 after no longer needed” retention period is set by the LGS-1, which is the master list of record retention terms for government agencies in New York.
Here is the LGS-1’s listing for security footage:
When developing a security footage/library user record policy, it is important to keep this non-existent retention period for boring footage in mind.[7]
Why is that important? If a request has been received for footage that is already deleted (because your library did not identify a need to retain it), the library has no ability to fulfill the request and has no culpability for not having the footage.
If the library retains the footage for a set time (for instance, 30 days) and then routinely deletes it, but a legitimate demand to retain the footage is received prior to the footage being deleted, the footage must be retained as having a “potential legal use.”
For this reason, it is important for public libraries with security systems to set a retention period for security camera footage and to ensure they are deleting the recordings exactly as required by the policy. This is because if a public library gets a request for the footage, and the library has the footage, it must be preserved, even if it is past its retention period… and even if it is regarded as a library user record.
Note that I say it must be “preserved,” not that it must be “disclosed.” Disclosure is only required after a library user grants their written permission or the library receives a subpoena or court order. Assessing when the library is compelled to provide the record is another job for the library’s attorney.[8]
Returning to the member’s question (“I would like to know what limitations and obligations we have in this civil matter with regard to patron privacy”), the answer is: the library cannot go wrong by assuming that the record cannot be disclosed without a subpoena or court order and not releasing it until the library’s attorney has assessed the matter and provided written advice.
Here are just a few of the variables that make caution and taking your time wise:
- The “litigation hold” demand might not be legitimate;[9]
- The case could be settled in between the time the library gets the request and is ready to fill it;[10]
- The person the footage pertains to could attempt to “quash” the subpoena;
- A party could try to appeal the court order directing that the record be provided;
- If the footage is needed by the library user it pertains to, that person could sign a release, but there is no obligation on the part of the library to provide the record;
- The library may need to address footage that shows one or more other person(s) in the same frame as the person(s) to whom a subpoena pertains.
When a library director (or another lucky employee) receives a request like this, the best response is to draw a deep breath, call your board leadership and/or library system to develop a response plan,[11] or reach out to the library’s attorney.[12] If the footage that was requested still exists but is scheduled for deletion, it should be preserved immediately.[13] Other than that, nothing should happen quickly.
The good thing to remember is that no matter what, libraries in New York[14] are well-positioned to go to the mat for library user privacy—a notion that in 2025 may seem quaint but grows more important with every passing day.
Thank you for a great question.
[1]^ They need money to give the tow truck guy, and he only takes Venmo! Send $1,000.00 or they have to spend the night on the road! This is the stuff that is happening now. Aaargh, sometimes I just want to go full Luddite.
[2]^ Or, as we used to call it back in the day, “RageMaker,” as it defied instructions to properly kern the alignment of a college newspaper heading. Take that, outdated 90’s software! No wonder you are being replaced with AI.
[3]^ No lawyer is paying the bills by simply verifying that a letter from a law firm is legit.
[4]^ FOIL stands for the “Freedom of Information Law,” of course. FOIL what obligates government agencies in New York to share most records with the public.
[5]^ See CPLR Section 4509 here: https://www.nysenate.gov/legislation/laws/CVP/4509
[6]^ Or whatever you call the policy governing user confidentiality. I like “Assurance of Patron Privacy and Non-disclosure of Library Records,” but I know that sounds stuffy.
[7]^ “Boring” as in it does not have content the library knows is relevant to a potential legal issue, like an injury, harassment claim, property damage, etc.
[8]^ For library leaders concerned about the bill, this shouldn’t take too much time. Unless there are complications, it should be about an hour or so, and the library should get the answer in writing.
[9]^ Letters like the once described by the member are often, but not always, called “litigation hold” or “duty to preserve” letters.
[10]^ I had this happen once. All that caution, and then the case was dropped. It was good that things ended before library records had to be disclosed, but also kind of anti-climactic.
[11]^ DO NOT EMAIL in substance just yet, as you could be adding to the written trove of evidence an attorney is seeking.
[12]^ You can write to your attorney under assurance of attorney-client privilege, so writing to them is A-okay.
[13]^ If the request is insufficient to identify which footage or area of the library is needed, save everything from the date(s) listed until the request can be narrowed or disregarded.
[14]^ That includes public libraries, association libraries, school libraries, and libraries at colleges and universities.
